Cyber Security
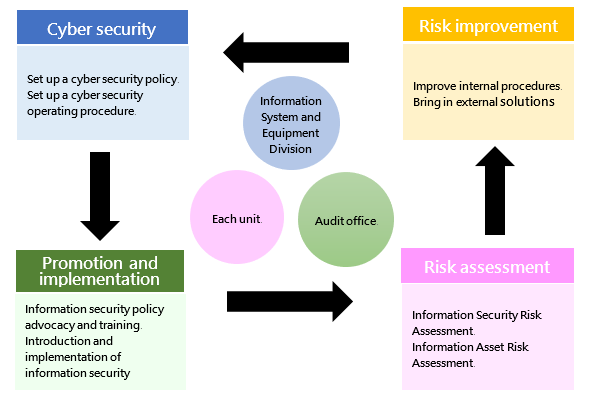
1. Cyber security management strategy and structureThe unit in charge of information security of the Company is the Information System and Equipment Division, which is staffed with one director and several professional information personnel, is responsible for formulating internal information security policies, planning and implementing information security operations, and the promotion and implementation of information security policies, reports the Company's information security governance overview to the Audit Committee.
The Company's information security supervision and inspection unit is the Audit Office, which is staffed with one audit director and several dedicated auditors, is responsible for supervising and inspecting the implementation of internal information security matters. If relevant deficiencies are found in the inspection, the inspected unit will be required to submit relevant improvement plans and specific actions, which will be tracked for the improvement results so as to reduce internal information security risks.
Organizational operation mode - The PDCA cycle management is adopted to ensure the achievement of reliability goals and continuous improvement.
 2. Cyber security policy
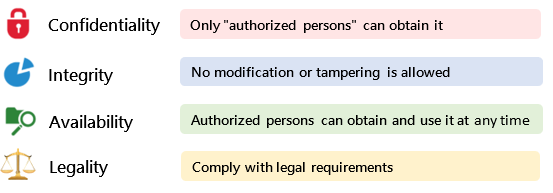
2. Cyber security policyIn order to implement the effective operation and implementation of UVB's various information management systems, we maintain the confidentiality, integrity, and availability of important information systems so as to ensure the safe operations of information systems, equipment, and networks.
UVB has established an information security management mechanism, including the following three major items:
(1) System norms: Formulate the Company's information security management systems and guidelines, and standardize the information-related operation behavior of colleagues.
(2) Application of new technology: Import and build information security management related software and hardware, and implement information security management measures.
(3) Personnel training: Regularly conduct information security education and training to enhance the information security concept of all colleagues and implement various information security measures.
Described as follows:
• System norms: The Company has formulated a number of information security management guidelines and systems to regulate the information security behavior of the Company's personnel. It regularly inspects whether the relevant systems conform to the changes in the operating environment every year, and makes adjustments in a timely manner according to needs.
• Application of new technology: In order to prevent various internal and external information security threats, in addition to adopting a multi-layer network architecture design, the Company also builds various information security protection systems and mechanisms, such as high reliability architecture (HA) of high availability, host environment backup, data backup (transaction records, differential backup, and full backup), off-site backup mechanism to improve the security of the overall information environment. In addition, in order to ensure that the operation behavior of internal personnel conforms to the Company's system norms, asset management system tools are also introduced to implement equipment and personnel information security management measures.
• Personnel training: The Company regularly organizes information security education and training courses and establishes an online learning (E-Learning) system to enhance internal personnel information security knowledge and professional skills.
| Information Security Management Measures | ||
|---|---|---|
| Type | Description | Relevant operations |
| Authority management | Management measures for personnel account, authority management, and system operation behavior | Personnel account permission application management and review Regular personnel account permissions inventory |
| Access control | Control measures for personnel access to internal and external systems and data transmission channels | Internal / external access control measures Operation behavior tracking record |
| External threat | Internal potential weaknesses, poisoning channels, and protective measures | Host / computer vulnerability inspection and update measures Virus protection and malware detection Malicious attacks prevention equipment |
| System availability | System availability status and handling measures when service is interrupted | Routine inspection of computer room System / network availability monitoring and reporting mechanism Response measures to service interruption Information backup, local / remote backup mechanism, regular data restoration test Host restore test Regular disaster recovery drills |
Cyber Security Drills and Training Activities in 2024
- In May 2024: Conducted "Information Security Awareness" on-the-job training courses for current employees, with a total of 292 participants as of December 31, 2024.
- In the year 2024: Held "Information Security Awareness" onboarding training courses for new employees, with a total of 75 participants as of December 31, 2024.
- In the year 2024: Conducted "Personal Data Protection Act" onboarding training courses for new employees, with a total of 75 participants as of December 31, 2024.
Cyber Security Drills and Training Activities in 2025
(1) Social Engineering Exercise
- Date: August 5, 2025
- Scope: All employees at the Nangang Office
- Number of Participants: 119
- Number of Employees Who Did Not Pass: 14, all of whom have subsequently completed the required information security courses and assessments.
(2) Cybersecurity Awareness Campaign
- Date: 2025 (May 15; October 30; November 6; November 28)
- Scope: All employees at the Nangang office and retail stores
- Number of Participants: 409
(3) Cybersecurity Training Program for In-service Employee
- Date: June 26, 2025
- Scope: All employees at the Nangang Office and retail stores
- Number of Participants: 319
(4) Cybersecurity Training Program for New Employees
- Period: 2025
- Scope: New Employees at the Nangang Office and retail stores
- Number of Participants: 91
Implementation Status of Cybersecurity–Related Meetings in 2025:
- ISO 27001–Related Meetings: A total of 14 meetings were held with relevant departments and external consultants.
- Information Security Task Force Meetings: 1 information security task force meeting was convened.
- In August 2023, the Company implemented the ISO/IEC 27001 Information Security Management international standard and obtained third-party certification. This strengthened the Company's capability to respond to information and communications security incidents, ensuring the confidentiality, integrity, availability, and legal compliance of corporate information assets, as well as the protection of customers' personal data.
- In August 2025, the Company successfully completed the ISO/IEC 27001 certification upgrade. In accordance with the updated requirements, the Company conducted vulnerability and risk assessments for servers, networks, and applications; established a document encryption mechanism; and planned secure cloud services to reduce the risk of sensitive data leakage. The Company also performs regular external system vulnerability assessments, penetration testing, and network risk-scanning to ensure timely remediation and system security. Periodic disaster recovery drills are conducted to strengthen data backup mechanisms and incident response capabilities, thereby ensuring business continuity.
- The current certificate is valid from August 22, 2025 to October 31, 2026.
 6. Professional Development and Certification of Cyber Security Manager and Personnel
6. Professional Development and Certification of Cyber Security Manager and PersonnelCyber Security Manager:
- December 2024 to February 2025: Courses organized by the Taiwan Academy of Banking and Finance, including "Guidelines for Information Security Management of Listed and OTC Companies," "Explanation of Information Security Incidents and Preventive Measures," and "Information Security Awareness, Essential Knowledge, and Responsibilities," totaling 6 hours.
- April to June 2025: "ISO/IEC 27001:2022 Information Security Management System Internal Auditor Training," totaling 6 hours.
Cyber Security Personnel:
- March 2024: Completed a 12-hour iPAS Information Security Engineer course and obtained the Ministry of Economic Affairs Industry Talent Competency Certification for "Information Security Engineer—Basic Competency."
- September 2024: Completed a 40-hour ISO/IEC 27001:2022 Information Security Management System (ISMS) Lead Auditor Training Course and obtained certification. This certification is valid for five years and is applicable to the CQI/IRCA Auditor certification scheme.
- December 2024 to February 2025: Courses organized by the Taiwan Academy of Banking and Finance, including "Guidelines for Information Security Management of Listed and OTC Companies," "Explanation of Information Security Incidents and Preventive Measures," and "Information Security Awareness, Essential Knowledge, and Responsibilities," totaling 6 hours.
- April to June 2025: "ISO/IEC 27001:2022 Information Security Management System Internal Auditor Training," totaling 6 hours.
- July to August 2025: "Cloud Computing and AI Information Security Program" under the Industry Talent Investment Program, totaling 36 hours.